Cyber security is not new, yet the level of awareness is still low and many individuals are not diligent about protecting their digital life. It is only with the recent SingHealth data breach – also known as Singapore’s largest ever cyber-attack – that people are sitting up and paying greater attention than ever to be safe online. Are you trying to figure out how and what you can take precaution against when you are online? Technical jargons of the digital world give us headaches too, so don’t worry! We will share with you the six most common cyber threats in simple human language and how you can reduce online risks. Read on!
1. Hackers
A trespasser in the virtual world, a hacker is a computer expert that breaks into a computer system or network. Many of us are familiar with the term ‘hacker’, but do you know the true implications of what a hacker can do? Before we share with you, you should know that hackers are also known as Black Hats and White Hats (sometimes Grey Hats too) but don’t ask us how the names are derived. The colour preferences go beyond fashion considerations, and actually define the nature of the work that they do.
A Black Hat hacker may steal your data, extort ransoms and seize control of your computer with criminal intent! This can be done as easily as accessing webcams to secretly record victims and blackmailing them thereafter with incriminating information caught on the webcam. In Singapore, 5,430 cybercrimes were reported last year, out of which ~760 cases falls under cyber extortion!
However, before you start thinking that all hackers are bad – the world of hacking is not shrouded in total blackness. On the other side of the spectrum lies the White Hat hacker, whom is better known as an ethical hacker that improves security by exposing vulnerabilities before Black Hat hackers detect and exploit the situation.
Point to note: Be careful of the Black Hat hacker and adopt good cyber security practices like covering up your webcam with a sticker.
2. Malware
Short for malicious software, malware reflects its namesake literally, and refers to any software designed to cause damage to your computer, server or network. This is one of the most common cyber threats, which covers viruses, worms, Trojan horse, spyware, etc.
Viruses occurs when an infected program is launched. It usually keeps a low profile to spread widely without being detected, and is likely to steal information. Download links are one of the places where these viruses lurk, hence you may want to think twice before downloading that free drama episode from an uncertified source! Also, do be mindful of installing plug-in! Watching a video that required a special software (plug-in) on a social app? There may be a virus, which can capture and record passwords used to log into your computer.
Worms are similar to viruses but they don’t need to launch an infected program and the scary part is they can self-replicate! Worms can cause some harm to the network, such as consuming bandwidth, which will make your computer super slow. They may sound harmless as compared to viruses but when the worms are encoded, you need to worry about “payload”.
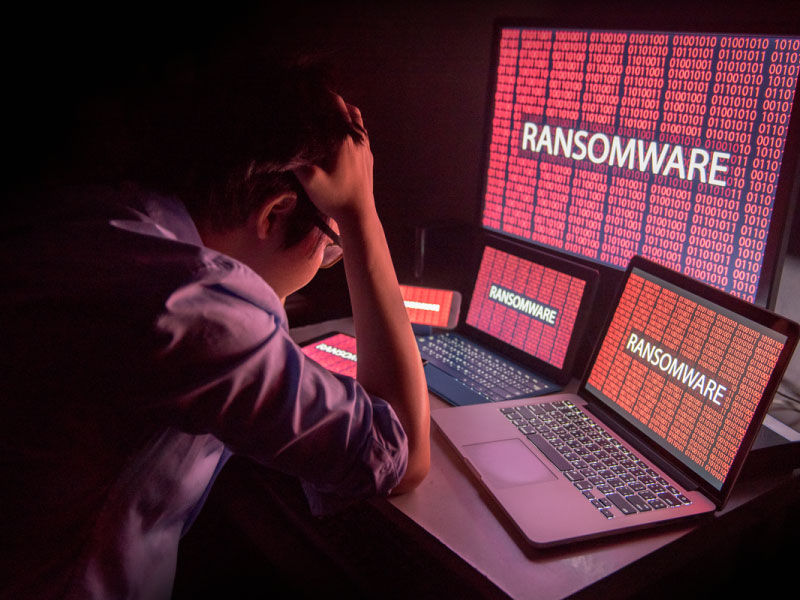
Payload can delete files on a host system, encrypt files in a ransomware attack or steal data such as passwords or confidential documents. We heard that the most common payload for worms is to install a backdoor. That’s kind of like opening your virtual door secretly, so that the worm author can control your computer remotely. To avoid worms, be careful of opening unexpected mail or visiting websites that are linked to such emails.
Spyware typically spies and steals, but could do more damage such as cyber extortion. We cannot emphasize more on covering up your webcam with a sticker because a webcam can be accessed by hackers to secretly record you. Incriminating evidence caught on webcams has been used to blackmail people and made them “slaves”. Spyware typically installs itself on a system without the user’s knowledge such as bundling itself with desirable software.
Trojan horse is like its namesake. It conceals, and then steals. You may be duped into filling up an unsuspicious email attachment or click on some fake advertisement on social media. Many forms act as a backdoor (again!), which allows a hacker to have unauthorised access to the affected computer. An attacker may easily access users’ personal information such as banking information, passwords, or personal identity. Note that ransomware are usually carried out using a Trojan horse.
Credits: GIPHY
Point to note: Don’t be a cheapskate and download free ‘things’ from uncertified online sources, and be alert when it comes to installing software in your system.
3. Pharming
In real life, we would not usually enter a stranger’s home but we often do this in the virtual world, unknowingly. Even if we are cautious, there’s the hacker that may install a virus or Trojan horse on your computer that changes the host’s file to direct you towards a fake website. Pharming attempts to redirect website traffic and bring you to a fake website. When this happen, your computer will be susceptible to viruses or Trojans horses, or worse! Your personal and financial information may be stolen for use in identity theft.
The bad news is if hackers do their job well, it‘s quite impossible to recognise a fake, data-stealing site. The good news is there are still a few things that you can lookout for:
- Always check the URL of the website to make sure it is spelt correctly
- Ensure that the URL has been changed to “https”; the “s” stands for “secure”
- Use security software to ensure the sites you visit are trustworthy
- Get Personal Cyber Insurance that covers losses deriving from cyber fraud
4. Phishing

Sensitive data such as your personal identification information, banking and credit card details and even password can be used to access important accounts, which can result in identity theft and financial loss. In case you are wondering why would anyone wants to be you, think again before you receive a court summon or visit by debtors for crimes or debts that you are unaware of committing!
To protect your online passwords, here are three basic but important things to note:
- Use a strong password (preferably 12 characters or more)
- Use multifactor authentication
- Use different passwords for different accounts – you can use a password manager to keep track
5. Ransomware
6. Social engineering
This technical term is gaining popularity in recent years but it could possibly be the oldest trick in the world; using human psychology. Social engineering is the art of gaining unauthorised access to secured systems or personal date by impersonation, or tricks instead of through a software vulnerability. For example, a social engineer may pose as your cable television IT support person, to trick you into divulging your password. It could also be someone impersonating as your friend and contacting you via Facebook messenger to get ‘financial help’. Do not donate unwittingly to that ‘fake’ friend and suffer financial loss!
While we are on this topic, you should also be mindful of posting sensitive information on your social media accounts because you never know who is watching! New homeowners may think that it is fine to take a celebratory picture of your new house key and geo-tagging your new house but did you know that it is easy to duplicate a physical key from a photo?
Credits: GIPHY
Point to note: Don’t be too quick to trust, always stay calm and research before reacting. Also, think twice before uploading and geo-tagging that new home photo.
Personal cyber security starts with you
According to Hootsuite, 84% of the population in Singapore is online, and 93% of us use the Internet daily. On average, Singaporeans are online for 7 hours and 9 minutes. With one of the highest smart phone penetration in the world, we are very connected and very vulnerable to cyber-attacks. Last year, 5,430 cybercrimes were reported in Singapore with online cheating accounting for 82.7%, cyber extortion for 1.4%, and 15.9% of cyber-crime involving compromised social media and SingPass accounts, impersonation scams, ransomware, and etc.
It is up to individuals to do our due diligence for cyber security. Although there will always be events that are out of our control, we can take precaution such as getting cyber protection. The Personal Cyber Insurance, now available at Tiq Singapore, allows you and your family to stay safe online!
Key benefits of Personal Cyber Insurance policy include:
- Protection against financial losses that derive from cyber fraud
- Compensation for the extortion payment in the event of cyber extortion
- Reimbursement for restoration costs in the event of a malware attack or hacking
- Protection against expenses incurred to restore your identity in the event it is stolen for fraudulent purposes*
For more information, please visit: https://tiq.com.sg/personal-cyber-insurance